I just found this post relating to facility management and Reassessing Security Plans as Terrorist Networks Become Decentralized.
 While not talking specifics, there are aspects of all forms of security that can be implemented to improve your overall awareness of who is accessing your building without authorisation. The reality is your biggest weakness in your buildings security is not the technology. It’s the people legitimately working inside!
While not talking specifics, there are aspects of all forms of security that can be implemented to improve your overall awareness of who is accessing your building without authorisation. The reality is your biggest weakness in your buildings security is not the technology. It’s the people legitimately working inside!
The reality is all of us are guilty of not enforcing the procedures put in place to manage security.
Have you ever worked in an office where a person just walks in with a tool box and starts working?
Did you ask them for ID?
No – because you assume someone else has authorised them to be there.
I was working in a government building as an alarm technician back in the day when someone came through and washed all the windows. He came in with his bucket, a rag in the back pocket and squeegee, cleaned the internal windows and left. About 20 minutes later people started noticing their purses missing from their bags.
Asking around the office, no-one took enough notice of the person to identify them and if they did sign in, no ID was checked.
There are many ways to walk into a building unchallenged
The best way to get into a building is to look like you should be there. Be confident about why you are there and most people will just accept it.
CCTV is a great deterrent but it is often not monitored so is only of use after the event. And if you have read the post about camera height and scene width, you will know that the chances of a usable image are slim unless the camera’s application was clearly defined.
So what is the best way to manage the threat?
As I mentioned, while there are many ways we can improve a buildings security, the biggest risk actually comes from the employees letting people in. This is not an intentional violation of security – Just the fact that if someone appears to know why they are there (confident and have a valid reason) many people will assume they have been authorised by someone else.
The best way I have found to manage this risk it to combine visitor management systems, access control and CCTV to work together as a solution rather than 3 separate areas of electronic security.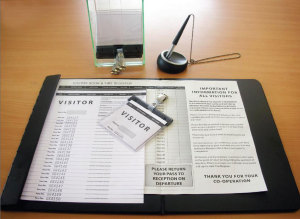 A typical CBD building will have some form of access control. This might be a card to release a door or a receptionist that signs people in. In either case, visitors are typically issued a “Visitor Tag“, which is just a piece of paper you could have randomly written any name on and very few people actually check anyway. In fact, as many sign-in books are available from the Amazon store, why not just keep one in the car and make your own tag so you can bypass the reception stage.
A typical CBD building will have some form of access control. This might be a card to release a door or a receptionist that signs people in. In either case, visitors are typically issued a “Visitor Tag“, which is just a piece of paper you could have randomly written any name on and very few people actually check anyway. In fact, as many sign-in books are available from the Amazon store, why not just keep one in the car and make your own tag so you can bypass the reception stage.
Step 1 is to have a better system to identify who is on site
This means everyone in the building should have an ID tag and have it visible.
For visitors this is required to be returned and signed in at the end of their working day. Not just thrown in a box with all the others. It is common for contractor to simply leave site with their ID and no-one ever follows it up. Using a visitor management software we can improve on this, allowing the capture of the visitors details, including a photo and printing an ID for them on each visit with a clearly visible valid date. This system still requires a person to take responsibility in entering the data and following up people that did not sigh out.
This is where a combined access control and visitor management system starts to show its advantages. With our advanced visitor management they are issues an access card with the photo ID when they sign in. On departure they physically need to drop their access card into a slot, which registers the card holder as off site and releases the exit door. If they haven’t registered as leaving site by their due time, an automated email alert will be generated to advise of this breach.
What happens if they do take an ID or reproduce a copy?
We have time sensitive ID tags, which change their image over time. So when issued, It has the persons details and a date / time they are authorised to be on site.
After the time period, the tag will change in appearance to a very visual indicator that they are not authorised.
So we have the visitor management sorted – What about getting staff to enforce this?
This is actually the bigger problem – you need to re-enforce to staff that they MUST wear an ID and to question ANYONE not displaying theirs.
A feature of the visitor management is to present various random challenges and manage competencies.
For example
- a competency can be that all staff have completed a security awareness in the past 3 months. If this expires, they are restricted in access until they do so.
- through random selection, the access system can require any person accessing an area to wait until security has viewed them through a CCTV camera to see if they have their ID displayed and they are actually the person who was issued the card.
It’s a subject I could go on about for hours (yes I’m a nerd) but I wont. Well not today.
But I will add to this topic based on my experience and any questions you may have. So do leave a comment below.
